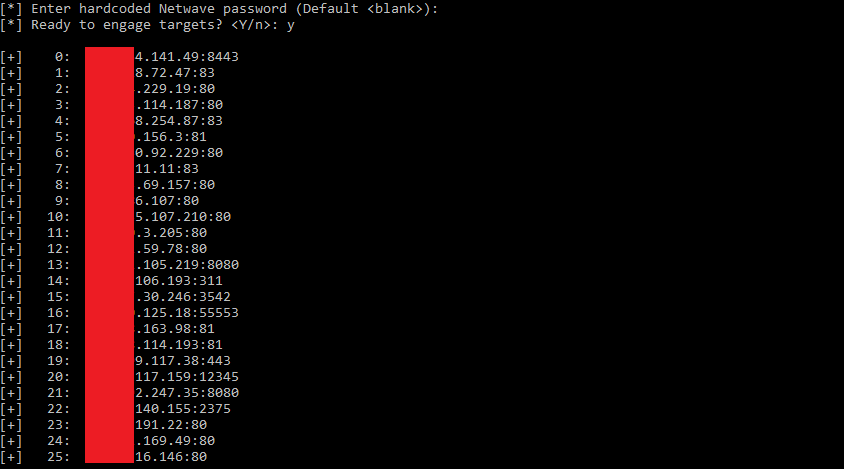
Security researchers have identified a vulnerability that makes it easy to guess the default factory administrator passwords on hundreds of printer models globally, including devices from Brother and Fujifilm.
The issue was discovered by specialists at Rapid7. They explained that many printers are shipped with a factory-set administrator password generated using a predictable algorithm. Their findings revealed that this algorithm could be exploited using a specific vulnerability for 689 Brother printer models, as well as 53 models from Fujifilm, Toshiba, and Konica Minolta.
The vulnerability, tracked as CVE-2024-51978, allows attackers to determine the factory-assigned administrator password if the user has not changed it. Successfully exploiting this flaw grants unauthorized access to the printer`s system and potentially to the internal network it is connected to.
Rapid7 has reported the problem to the affected manufacturers. Brother and other companies have since released firmware updates to address the vulnerability. However, these patches primarily benefit newly produced devices. Security experts strongly recommend that all consumers immediately change the default administrator password on their printers, especially if it hasn`t been updated since the device was acquired.
Action Required: If you own a printer from Brother, Fujifilm, Toshiba, or Konica Minolta, check your device`s administrator settings and change the default password to a strong, unique one.